Cyberattack that shut down U.S. pipeline linked to criminal gang

- Share via
NEW YORK — The cyber-extortion attempt that has forced the shutdown of a vital U.S. pipeline was carried out by a criminal gang known as DarkSide, which cultivates a Robin Hood image of stealing from corporations and giving a cut to charity, two people close to the investigation said Sunday.
The pipeline’s shutdown has stretched into its third day, with the Biden administration loosening regulations for the transport of petroleum products on highways as part of an “all hands on deck” effort to avoid disruptions in the nation’s fuel supply.
Experts said gasoline prices likely would not be affected if the pipeline got back to normal in the next few days but that the incident — the worst cyberattack to date on critical U.S. infrastructure — should serve as a wake-up call to companies about the vulnerabilities they faced.
The pipeline, operated by Georgia-based Colonial Pipeline, carries gasoline and other fuel from Texas to the northeastern U.S. It delivers roughly 45% of fuel consumed on the East Coast, according to the company.
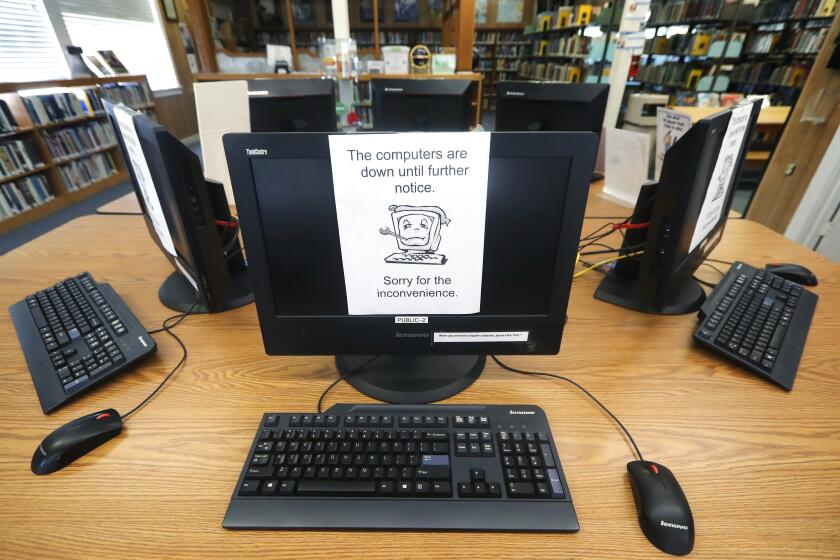
It was hit by what Colonial called a ransomware attack, in which hackers typically lock up computer systems by encrypting data — paralyzing networks — and then demand a large ransom to unscramble it.
On Sunday, Colonial Pipeline said it was actively in the process of restoring some of its IT systems. It said it remained in contact with law enforcement and other federal agencies, including the Department of Energy, which is leading the federal government response. The company did not say what was demanded or who made the demand.
A ransomware attack at the Newhall School District over the weekend has put online learning on hold for roughly 6,000 students.
However, two people close to the investigation, speaking on condition of anonymity, identified the culprit as DarkSide. It is among ransomware gangs that have “professionalized” a criminal industry that has cost Western nations tens of billions of dollars in the past three years.
DarkSide claims that it does not attack hospitals and nursing homes, educational or government targets and that it donates a portion of its take to charity. It has been active since August and, typical of the most potent ransomware gangs, is known to avoid targeting organizations in former Soviet-bloc nations.
Colonial did not say whether it had paid or was negotiating a ransom, and DarkSide neither announced the attack on its dark-web site nor responded to an Associated Press reporter’s queries. The lack of acknowledgment usually indicates a victim is either negotiating or has paid.
On Sunday, Colonial Pipeline said it was developing a “system restart” plan. It said its main pipeline remained offline but some smaller lines were now operational.
The recently revealed hack of government networks, believed to have been conducted by Russia, is a historic act of espionage and revealed severe leaks in the U.S.’ cyberdefense, says cryptographer and security expert Bruce Schneier.
“We are in the process of restoring service to other laterals and will bring our full system back online only when we believe it is safe to do so, and in full compliance with the approval of all federal regulations,” the company said in a statement.
Commerce Secretary Gina Raimondo said Sunday that ransomware attacks were “what businesses now have to worry about,” and that she would work “very vigorously” with the Department of Homeland Security to address the problem, calling it a top priority for the Biden administration.
“Unfortunately, these sorts of attacks are becoming more frequent,” she said on CBS’ “Face the Nation.” “We have to work in partnership with business to secure networks to defend ourselves against these attacks.”
She said President Biden was briefed on the attack.
Just days after data on a new COVID-19 vaccine were unlawfully accessed by hackers, the European Union proposes revamping its cybersecurity rules.
“It’s an all-hands-on-deck effort right now,” Raimondo said. “And we are working closely with the company, state and local officials to make sure that they get back up to normal operations as quickly as possible and there aren’t disruptions in supply.”
The Department of Transportation issued a regional emergency declaration Sunday, relaxing hours-of-service regulations for drivers carrying gasoline, diesel, jet fuel and other refined petroleum products in 17 states and the District of Columbia. The declaration allows them to work extra or more flexible hours to make up for any fuel shortage related to the pipeline outage.
One of the people close to the Colonial investigation said the attackers also stole data from the company, presumably for extortion purposes. Sometimes stolen data are more valuable to ransomware criminals than the leverage they gain by crippling a network, because some victims are loath to see sensitive information of theirs dumped online.
Security experts said the attack should be a warning for operators of critical infrastructure — including electrical and water utilities and energy and transportation companies — that not investing in updating their security put them and their customers at risk of catastrophe.
Ed Amoroso, CEO of TAG Cyber, said Colonial was lucky that its attacker was at least ostensibly motivated only by profit, not geopolitics. State-backed hackers bent on more serious destruction use the same intrusion methods as ransomware gangs.
“For companies vulnerable to ransomware, it’s a bad sign because they are probably more vulnerable to more serious attacks,” he said. Russian cyber warriors, for example, crippled the electrical grid in Ukraine during the winters of 2015 and 2016.
Cyber-extortion attempts in the U.S. have become a death-by-a-thousand-cuts phenomenon in the past year, with attacks forcing delays in cancer treatment at hospitals, interrupting schooling and paralyzing police and city governments.
Tulsa, Okla., this week became the 32nd state or local government in the U.S. to come under ransomware attack, said Brett Callow, a threat analyst with the cybersecurity firm Emsisoft.
The attack appears to have been intended to slow the agency’s systems down, but didn’t do so in any meaningful way, said the people, who asked for anonymity to discuss an incident that was not public.
Average ransoms paid in the U.S. jumped nearly threefold to more than $310,000 last year. The average downtime for victims of ransomware attacks is 21 days, according to the firm Coveware, which helps victims respond.
David Kennedy, founder and senior principal security consultant at TrustedSec, said that once a ransomware attack was discovered, companies had little recourse but to completely rebuild their infrastructure, or pay the ransom.
“Ransomware is absolutely out of control and one of the biggest threats we face as a nation,” Kennedy said. “The problem we face is most companies are grossly underprepared to face these threats.”
Colonial transports gasoline, diesel, jet fuel and home heating oil from refineries on the Gulf Coast through pipelines running from Texas to New Jersey. Its pipeline system spans more than 5,500 miles, transporting over 100 million gallons a day.
Iran has not lost its appetite for asymmetric cyber conflict as a means of confronting the United States.
The Justice Department has a new task force dedicated to countering ransomware attacks.
Although the U.S. has not suffered any serious cyberattacks on its critical infrastructure, officials say Russian hackers in particular are known to have infiltrated some crucial sectors, positioning themselves to do damage if armed conflict were to break out. There is no evidence that the Kremlin benefits financially from ransomware, but U.S. officials believe President Vladimir Putin savors the mayhem it wreaks in adversaries’ economies.
Iranian hackers have also been aggressive in trying to gain access to utilities, factories and oil and gas facilities. In one case in 2013, they broke into the control system of a U.S. dam.
More to Read
Sign up for Essential California
The most important California stories and recommendations in your inbox every morning.
You may occasionally receive promotional content from the Los Angeles Times.