CIA unit that crafts hacking tools didn’t protect itself, report says
- Share via
WASHINGTON — A specialized CIA unit that developed sophisticated hacking tools and cyberweapons didn’t do enough to protect its own operations and wasn’t prepared to adequately respond when the secrets were stolen, according to an internal report prepared after the worst data loss in the intelligence agency’s history.
“These shortcomings were emblematic of a culture that evolved over years that too often prioritized creativity and collaboration at the expense of security,” according to the report, which raises questions about cybersecurity practices inside U.S. intelligence agencies.
Sen. Ron Wyden (D-Ore.), a senior member of the Senate Intelligence Committee, obtained the redacted report from the Justice Department after it was introduced as evidence in a court case this year involving the stolen CIA hacking tools.
He released it Tuesday along with a letter he wrote to new national intelligence director John Ratcliffe, asking him to explain what steps he’s taking to protect the nation’s secrets held by federal intelligence agencies.
The October 2017 report, whose findings were first reported by the Washington Post, examined the theft one year earlier of sensitive cyber tools the CIA had developed to hack into the networks of adversaries.
The document is dated months after WikiLeaks announced that it had acquired tools created by the CIA’s specialized Center for Cyber Intelligence. The antisecrecy website published comprehensive descriptions of 35 tools, including internal CIA documents associated with them, according to the report.
The report describes the spring 2016 theft as the largest data loss in agency history — compromising at least 180 gigabytes to as much as 34 terabytes of information, or the equivalent of 11.6 million to 2.2 billion pages in Microsoft Word.
The agency did not realize the loss had occurred until the WikiLeaks announcement a year later, the report said. As officials scrambled to pinpoint who was responsible, they ultimately identified a CIA software engineer as a prime suspect who they said had left the agency on stormy terms after falling out with colleagues and supervisors and had acted out of revenge.
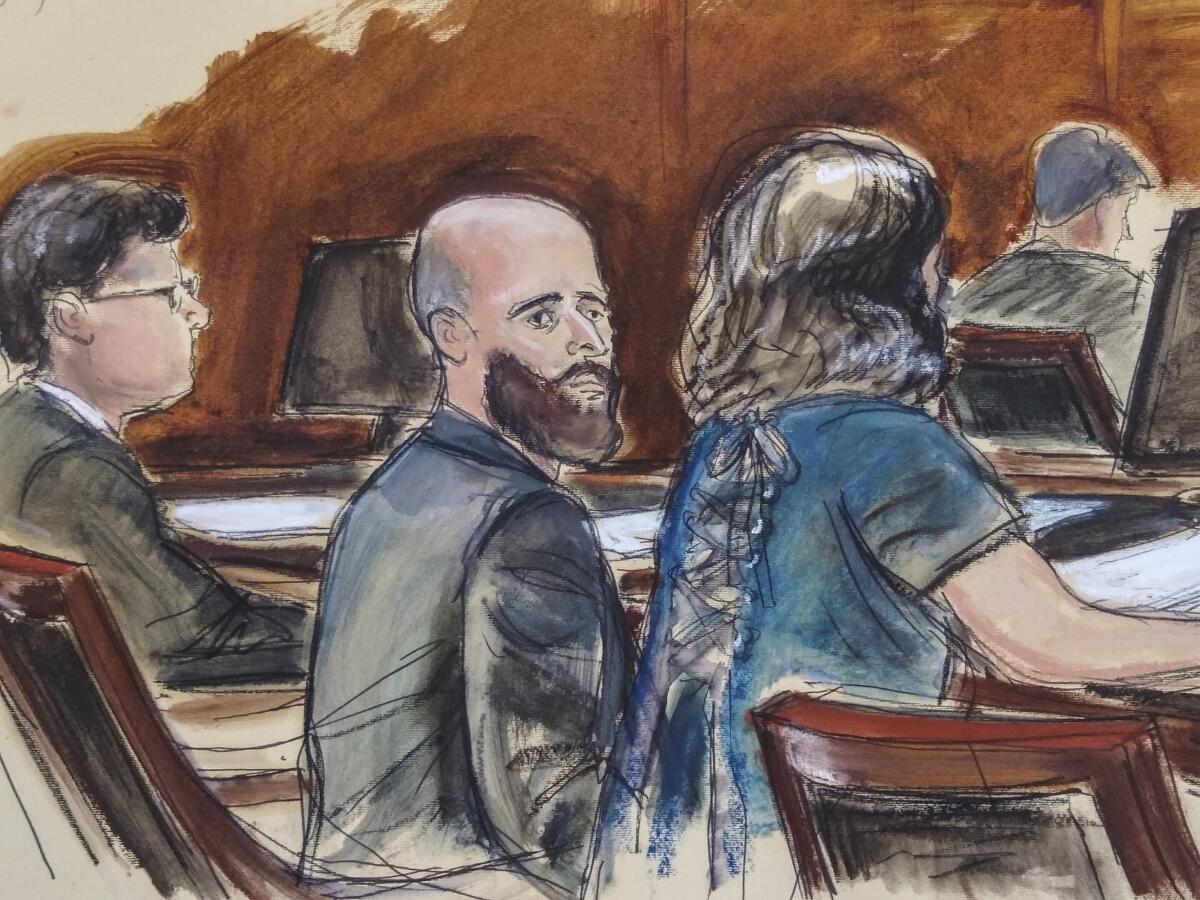
The former employee, Joshua Schulte, was charged by the Justice Department with stealing the material and transmitting it to WikiLeaks. But a jury deadlocked on those charges and convicted him in March of more minor charges after a trial in Manhattan.
The CIA report revealed lax cybersecurity measures by the specialized unit and the niche information technology systems that it relies upon, which are separate from the systems more broadly used by everyday agency employees. The report said that because the stolen data were on a system that lacked user activity monitoring, it was not detected until WikiLeaks announced it in March 2017.
“Had the data been stolen for the benefit of a state adversary and not published, we might still be unaware of the loss,” the report said.
The report, prepared by the CIA’s WikiLeaks Task Force, suggests the CIA should have been better prepared in light of devastating data breaches at other intelligence agencies. The hacking tools compromise occurred about three years after Edward Snowden, a former contractor for the National Security Agency, confiscated classified information about the NSA’s surveillance operations, and disclosed it.
“CIA has moved too slowly to put in place the safeguards that we knew were necessary given successive breaches to other U.S. Government agencies,” the report said.
Among the problems the report identified: sensitive cyber weapons were not compartmented, passwords were shared, and users had indefinite access to historical data.
CIA spokesman Timothy Barrett declined to comment on the report’s findings, but said the “CIA works to incorporate best-in-class technologies to keep ahead of and defend against ever-evolving threats.”
Sean Roche, a former associate deputy director for digital innovation at the CIA who testified at the Schulte trial, said that although the CIA did have a problem with one of its networks, “to say that the people at the CIA don’t take security seriously is not accurate. It’s completely inaccurate.”
Speaking Tuesday at a webinar hosted by the Cipher Brief, an online newsletter that focuses on intelligence, Roche likened the task force report to an after-accident report by the National Transportation Safety Board.
“This broke. This is what happened,” Roche said. “We need to make sure this doesn’t happen again. How is that not a healthy thing for an organization that doesn’t have a public eye into what it’s doing?”
The disclosure of the hacking tools featured prominently in Schulte‘s trial, with prosecutors portraying him as a disgruntled software engineer who exploited a little-known bac door in a CIA network to copy the hacking arsenal without raising suspicion.
“These leaks were devastating to national security,” Assistant U.S. Atty. Matthew Laroche told jurors. “The CIA’s cyber tools were gone in an instant. Intelligence gathering operations around the world stopped immediately.”
Defense attorney Sabrina Shroff argued that investigators could not be sure who took the data because the CIA network in question “was the farthest thing from being secure” and could be accessed by hundreds of people.
Ultimately, Schulte was convicted of contempt of court and making false statements after a four-week trial. The jury was unable to reach a verdict on the more significant charges.
More to Read
Sign up for Essential California
The most important California stories and recommendations in your inbox every morning.
You may occasionally receive promotional content from the Los Angeles Times.










